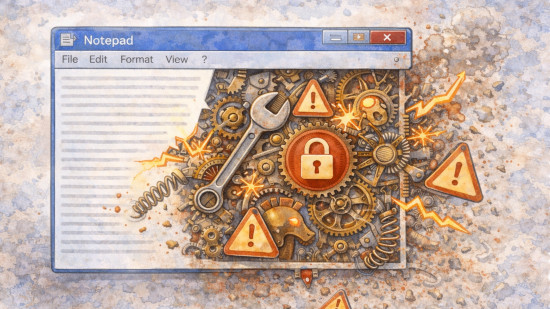
Notepad flaw shows why software bloat matters
- Notepad used to do one thing: edit plain text. Microsoft's insistence on adding formatting and Copilot led to a perfect example of why simplicity matters – an RCE vulnerability in its Markdown rendering.